ISO 27001:2022 Transitie
Onze ISO 27001 trainingen zijn onlangs aangepast naar de 2022 revisie die de standaard op het gebied van informatiebeveiliging heeft gekregen. Eén van onze trainers, Eppo Luppes, schreef voor PECB mee aan een paper over de transitie van 27001:2013 naar 27001:2022. Een deel van dit document lees je hieronder.
Naast de reguliere ISO 27001 Foundation, Lead Implementer en Lead Auditor trainingen verzorgen we tijdelijk ook speciale 2-daagse ISO 27001:2022 Transition trainingen die specifiek gaan over de wijzigingen in de standaard.
Door Roderick Commerell / PECB
III. ISO/IEC 27001 and the Reason for Its Revision
The past decade has witnessed a remarkable transformation in technology which significantly affected organizations and their information security management. Some of the technological changes that caused this transformation include cloud computing, the Internet of Things (IoT), Artificial Intelligence (AI), and blockchain. While these technologies provide better solutions for storing and processing data, they have also introduced new security concerns. As technology evolved, so did cyber threats. As such, organizations need to update their existing security practices to reflect the technology developments and current security threats.
ISO standards are usually revised at least once in every five years to ensure they remain adequate and relevant. The ISO/IEC 27001 was mainly revised to adapt to the ever-evolving information security challenges, which is why the most important changes were made in the information security controls listed in Annex A. The changes in clauses 4 to 10 are minor and were made mainly to ensure alignment with the harmonized structure for management system standards established by ISO and with the latest version of ISO/IEC 27002 published in 2022.
IV. What Has Changed in ISO/IEC 27001:2022?
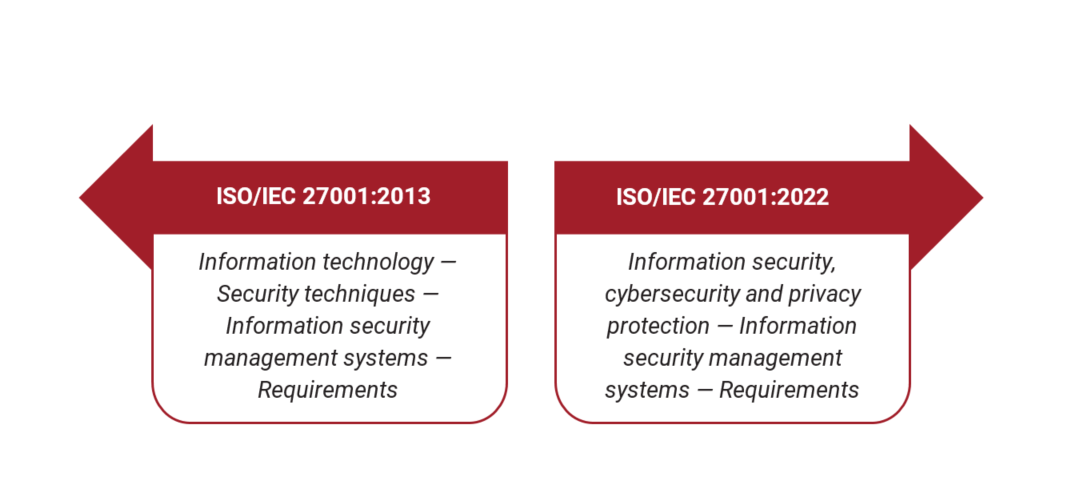
The title of the standard was changed to Information security, cybersecurity and privacy protection – Information security management systems – Requirements to align with the that latest edition of ISO/IEC 27002. The title of the revised standard now reflects its comprehensive scope, which includes both information security and cybersecurity. It is worth noting that while information security generally focuses on protecting information of all formats from unauthorized access, use, or modification, cybersecurity focuses on protecting digital assets from various threats, such as malware, hacking, and cyberattacks.
In clauses 4 to 10 the revisions were mainly technical, with the exception of a few requirements that were added. More significant changes were made in Annex A. The information security controls have been merged and updated based on the new categorization introduced by ISO/IEC 27002:2022, decreasing the number of controls from 114 to 93.
A. Changes in the Main Clauses of ISO/IEC 27001:2022
Clauses 4 to 10 of ISO/IEC 27001:2022 that provide the main requirements for an ISMS have changed slightly. A brief overview of those changes is provided below:
- Clause 4.2 Understanding the needs and expectations of interested parties added a requirement which states that organizations must determine the requirements of interested parties that need to be addressed through the ISMS.
- Clause 4.4 Information security management system, besides requiring organizations to establish, implement, maintain, and continually improve their ISMS, it requires to do the same for the processes related to the ISMS and their interactions.
- Clause 5.1 Leadership and commitment provides a clarification regarding the term “business” used in the standard, which is used to refer to “those activities that are core to the purposes of the organization’s existence.”
- Clause 5.3 Organizational roles, responsibilities and authorities has some minor changes and specifies that the roles and responsibilities regarding information security should be communicated within the organization.
- Clause 6.2 Information security objectives and planning to achieve them introduces two new requirements. Item d) of this clause requires to monitor information security objectives, whereas item g) requires to ensure they are available as documented information.
- Clause 6.3 Planning of changes is a new requirement of ISO/IEC 27001:2022. It requires organizations to carry out the changes to the ISMS in a planned manner.
- Clause 7.4 Communication has minor changes. Item (d) who shall communicate and item (e) the processes by which communication shall be effected have been merged to a new requirement: (d) how to communicate.
- Clause 8.1 Operational planning and control has been simplified and additional information has been provided on how to achieve the intended outcomes. This clause requires organizations to plan, carry out, and oversee processes that are essential to meet requirements by establishing criteria for the processes and implementing control of the processes in accordance with the criteria. The establishment of such criteria for ISMS processes allows organizations to evaluate the performance of the implemented processes and determine whether they conform to the established criteria.
- Clause 9.2 Internal audit has been divided into two subclauses: clause 9.2.1 General and clause 9.2.2 Internal audit programme to align with other management system standards; however, the requirements of this clause remain the same.
- Clause 9.3 Management review has been divided into three subclauses: clause 9.3.1 General, clause 9.3.2 Management review inputs, and clause 9.3.3 Management review results. This clause introduces a new requirement which states that the changes in needs and expectations of the interested parties that are relevant to the ISMS should be taken into account during management reviews. In addition, the new version of the standard refers to the outcomes of the management reviews as “results,” and requires organizations to assure that evidence of such results is available as documented information.
- Clause 10 Improvement has been rearranged but its content remains unchanged.
B. What Has Changed in Annex A of ISO/IEC 27001:2022?
Annex A of ISO/IEC 27001:2022 is a list of information security controls that aim to ensure the confidentiality, integrity, and availability of information and information assets. However, it should be noted that the information security controls listed in Annex A are not exhaustive and additional controls may be added as necessary by the organization. Annex A of ISO/IEC 27001:2022 has been updated and aligned with ISO/IEC 27002:2022.
The number of controls in ISO/IEC 27001:2022 has been reduced from 114 that were in the previous version to 93.
- 35 controls remained exactly as they were
- 23 controls were renamed
- 57 controls were merged into 24
- 11 new controls were introduced
The previous concept of the standard for grouping several controls within a control category with a common objective has been discarded, which is also reflected in the new control identifier (previous control A.5.1.1 has been changed to 5.1). While the previous version of the standard comprised of 114 controls categorized into 14 categories, the 93 controls of the new version have been restructured into four themes.
V. Overview of Annex A of ISO/IEC 27001:2022
The information security controls of Annex A of ISO/IEC 27001:2022 are categorized in four themes in alignment with ISO/IEC 27002:2022: organizational, people, physical, and technological.
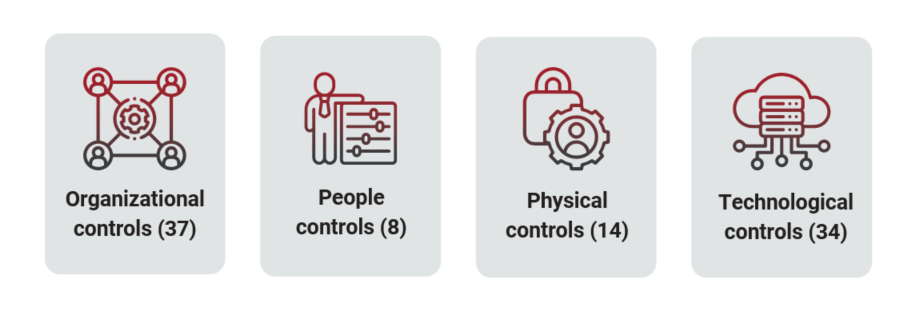
Annex A controls and their categorization are directly derived from ISO/IEC 27002:2022; however, organizations can customize their own view of controls based on organization’s context and needs. This helps organizations that seek to ensure compliance with ISO/IEC 27001:2022 to accelerate the process of comparing the necessary controls determined in the risk treatment plan with Annex A controls, as required by clause 6.1.3 Information security risk treatment. ISO/IEC 27002:2022 provides five attributes for each control: control type, information security properties, cybersecurity concepts, operational capabilities, and security domains.
Het volledige artikel vind je op de website van PECB.
3 jaren geleden